Since the launch of Let’s Encrypt CA in late 2015, obtaining TLS certificates has become cheap, quick and easy. Statistics this month showed Let’s Encrypt has yet issued nearly 1.8 million certificates. But it seems like this information hasn’t arrived at some website owners and API developers.
So I wrote a little script to poison DNS requests and let a little node.js script exchange all pictures requested by the victim (I will perhaps blog about this script another time). Sites and apps using TLS are perfectly fine, because they will reject connections to the fake web server without a valid certificate. Without transport security, things get mad.
For instance, I tested the script against a weather app on my phone and got this result:
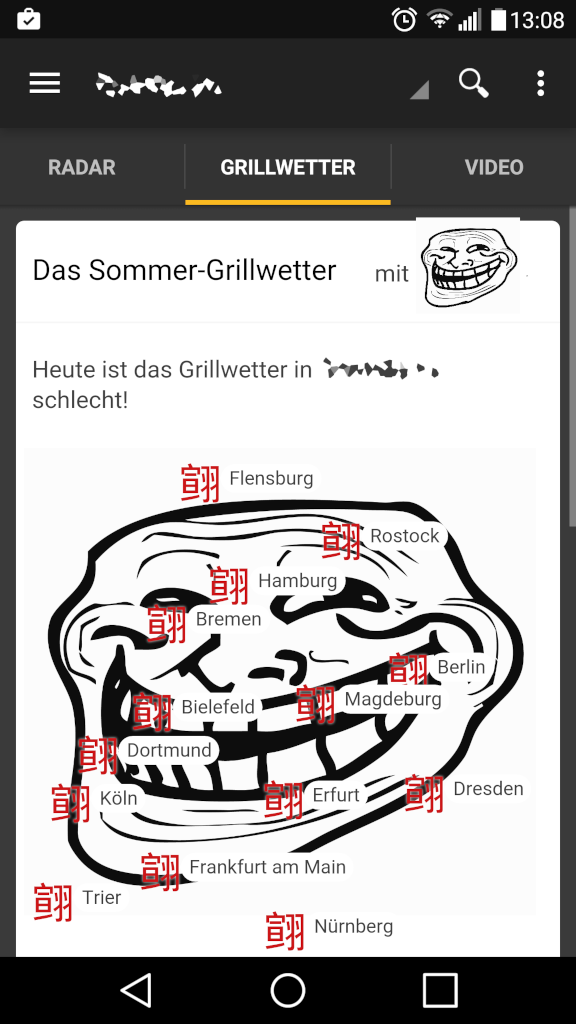
So the app seems not only to get its weather information over plain HTTP, but also loads a picture of a map of Germany from the internet (But why? Couldn’t you possibly include that into the app itself?). On my phone, I also found an app for viewing a popular webcomic and several apps from big German newspapers to be vulnerable.
Let’s think about this a little further. What if I not only exchanged pictures for funny ones, but also injected some malicious code? Knowing that thousands of apps out there don’t use a properly defined API but a simple WebView, someone could append malicious JavaScript code at the end of the HTML content. As free certificates are now available to anyone, there should be no more excuse for not having transport security enabled. And no, the ability to inject ads is not a valid excuse.
I contacted several app developers about that issue, and I’m waiting for replies, which I will maybe discuss here.
[Update 28.03.2016]
The guys from the weather app replied, stating they’re already using transport security in some parts of the app, and they’re currently working on a solution to enable it generally.